The word “decentralizationThe transfer of control from one central entity to numerous smaller entities. Generally, cryptocurrencies are decentralized. Every crypto transaction is... More” is one of those that can have a lot of meanings, fully depending on the context. In very simple terms, we can say that if a system is “decentralized”, then its control and/or its components are distributedA distributed system is made of components that are running on different networked computers, which communicate and coordinate their actions... More (split) between several parties. In theory, there’s not a single point of failure, and there’s not a single leader either.
In the software world (which includes cryptocurrencies), decentralization can be applied to numerous platforms at different levels. The computer scientist and entrepreneur Rohit Khare defines this complicated concept this way:
“A decentralized system is one which requires multiple parties to make their own independent decisions. In such a decentralized system, there is no single centralized authority that makes decisions on behalf of all the parties. Instead, each party, also called a peer, makes local autonomous decisions towards its individual goals which may possibly conflict with those of other peers. Peers directly interact with each other and share information or provide service to other peers.”
Now, as he mentions, decentralization is kind of chaotic if the peers have conflicts for a lack of consensus rules. Open decentralized systems, in which everyone can participate without any requirements (again, such as cryptocurrencies), can lead to welcome malicious peers who will attack the entire network or its participants. For example, malware inside files shared via P2P file-sharing apps.
For Rohit Khare, there are mainly two ways to prevent attacks in a decentralized system: a layer of reputation or a layer of credentials for every peer. Blockchain structures go further, though. To achieve consensus among all participants and do without the trust that we would put in centralized entities (such as companies or governments), special systems have been created with cryptographyCryptography is the mathematical basis for secure communication that allows only the sender and intended recipient of a message to... More.
A little about consensus and cryptos
Bitcoin and many others use Proof-of-Work (PoW). This one is an algorithm that develops a difficult math problem or riddle which must be solved to verify virtual transactions and create new coins. The device (usually the computer or ASIC machine) uses real-world electricity to solve this complex riddle. The new coins and transactions fees paid by users worldwide go as a reward for the miners —the people who set up, maintain, and paid the needed machines and energy to make the system work.

This way, a BitcoinBitcoin is the first decentralized digital currency. It was created in 2009, by an anonymous founder or group of founders... More transactionA cryptocurrency transaction is an entry on the blockchain ledger, noting sender, receiver and number of coins transacted. More is only valid if it’s approved by numerous miners and registered as it on the blockchainBlockchain is a type of database storing an immutable set of data, verifiable to anyone with access to it —through.... Therefore, if a malicious peer (minerMiners secure some blockchain networks by ordering crypto transactions into blocks and verifying the blocks of other miners. For this... More) tries to validate a fraudulent transaction, the results for them would only be self-damaging. They’d lose time and energy to no avail since the transaction won’t be approved by other miners. So, to get some results, a malicious actor or group would need to control at least 51% of the total mining power —which is known as a 51% attack.
However, the more miners (power) inside a blockchain, the more expensive are theoretical attacks. For example, the cost to make a 51% attack on Bitcoin is $1.5 million per hour. The possible profits don’t worth it because the system was designed exactly for that.
Other popular cryptocurrencies, such as Cardano (and Ethereum in the future), use another cryptographic system: Proof-of-Stake (PoS). In PoS systems, the figure of the “miner” is replaced by the “validator”. This validator, which can be anybody who wants to, won’t need any real-world resource. Instead, they lock a number of their own coins inside a special walletA crypto wallet is a user-friendly software or hardware used to manage private keys. There are software wallets for desktop... More. So, they can verify transactions and mint new coins, if necessary, and are rewarded for it.
We’ll back to these two systems and their decentralization (or not) ahead.
Types of decentralization
To understand a bit more about our cryptocurrencyA digital currency running on a blockchain and built with cryptography. Contrary to central-bank issued currency, cryptocurrency issuance rules are... More world and its goal of decentralization, the Ethereum founder Vitalik Buterin prepared an analysis about this. He considers that there are mainly three types of decentralization: architectural, political, and logical. Not all of them are present (or achievable) in cryptocurrencies since they implied different factors.

Architectural decentralization is about “how many physical computers is a system made up of” and “how many of those computers can it tolerate breaking down at any single time”. Political decentralization is about “how many individuals or organizations ultimately control the computers that the system is made up of”. And logical decentralization implies that the interface and data structures can be cut into several parts and still work.
In this line, his conclusion is:
“Blockchains are politically decentralized (no one controls them) and architecturally decentralized (no infrastructural central point of failure) but they are logically centralized (there is one commonly agreed state and the system behaves like a single computer).”
Of course, it’s easily assumed that no central company or organization is behind blockchains, so, they’re (in theory) politically decentralized. They’re also architecturally decentralized because are formed by numerous miners or validators with their own devices worldwide. But they need to be logically centralized (work as one) to reach consensus, i.e., to agree that a transaction is valid.
Why does decentralization matter?
In the cryptocurrency world, decentralization is a core feature. Architectural decentralization is necessary to increase the security and stability of blockchains. For example, if a miner (or a bunch of them) goes offline for any reason, the system will still work with few to no consequences. That, indeed, already happened with Bitcoin when China completely banned crypto mining last year.
It’s believed that at least 65% of all Bitcoin miners were operating in China back then. Despite the irrevocable fact that this isn’t much decentralized, when all those miners went offline amid the legal crisis, the network wasn’t affected on a large scale. The users experienced a slower network for a few days while the miners moved, and that was it. Architectural decentralization lets us have that advantage.
Political decentralization, for its part, let us have liberty over our money. If there’s not a single party controlling the system behind cryptocurrencies, that means they’re resistant to confiscation and censorship. The situation in Nigeria during the last two years is a great example. The government decided to impede the fund’s inflow from banks for the protesters since they can order the banks what to do.
However, the protesters still could receive funds in cryptocurrencies. Even when the government banned crypto, it was perfectly possible to exchange crypto in external services or directly between people, because they can’t control the blockchains (as they do with the banks).
Decentralization in blockchain systems
At this point, we can say that most cryptocurrencies make a nice try, but they’re not fully decentralized —yet. We still can’t assume that they’re controlled by no one, as Buterin stated. Every cryptocurrency has different levels of decentralization (or not), but we can talk about Bitcoin first.
As we mentioned before, 65% of the miners were concentrated in China until last year. Now, they’re more distributed worldwide, but we still might have an issue with mining poolsThousands of miners compete on the reward which is only paid once per block. Miners who join a mining pool... More. There are over 15,000 Bitcoin nodes worldwide, but only four mining pools control over 59% of the hashrate.
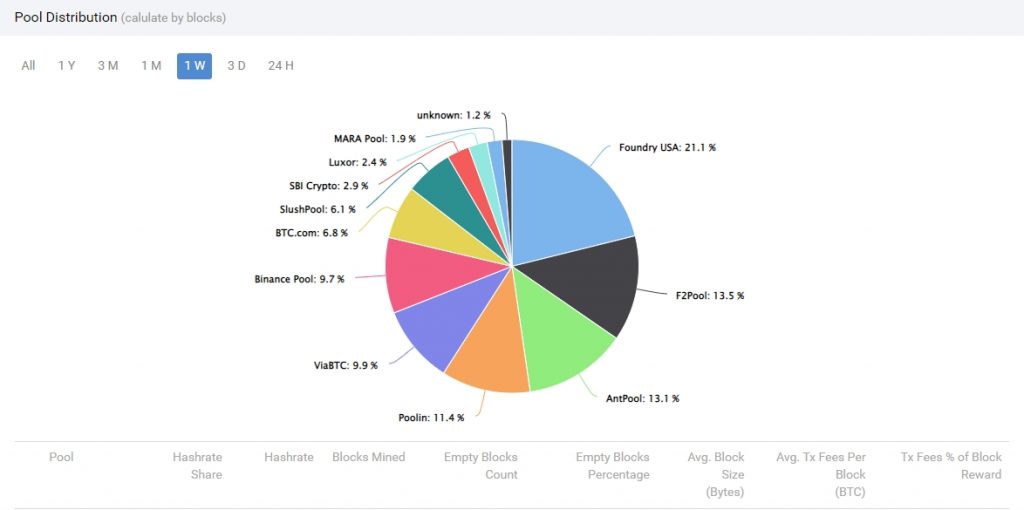
In theory, they could join to make a 51% attack —but the high costs make this less likely. It’s not the same for other cryptocurrencies with fewer miners and market capitalization, though. In DeepOnion (ONION), for example, a 51% attack would cost barely $1 per hour, and only one mining pool (Zpool) already has over 55% of the total hashrate. Of course, it would be much easier to attack than Bitcoin and other more robust currencies.
The code is something else to consider. Talking about Bitcoin again, only six men have access to the code of the main Bitcoin implementation, Bitcoin Core —used by 98% of the entire community [CoinDance]. Changing this code and compromising the entire network by somehow taking the keys from them wouldn’t be likely. The community would only take the last healthy version, make a fork (divide the network), and start from there again.
Nevertheless, there’s still a (tiny) chance that the Bitcoin Core code fails somehow, as it did in 2018. That’s why the use of other implementations might be welcome. There are, at least, six other software clients beyond Bitcoin Core, but they only account for 2% of the network together.
Centralization in PoS systems
Proof-of-Stake (PoS) systems have more centralization problems than PoW systems. They’re sometimes preferred because they don’t use big amounts of energy, and are considered, therefore, greener than PoW. But they have centralization issues that could jeopardize the system itself.

As we remembered before, the miner is replaced by the validator. All this validator needs to do is lock (stake) a number of its own coins, and will have the right to validate new blocks and get more coins for it. But the trick is the more coins they stake, the more right to vote they have. So, a millionaire member would be, in theory, more important than a small validator and would also take more coins.
Just as the analyst Lyn Alden explains it:
“It would be like a political system where you get a vote for every hundred dollars you have, and then also get paid a dollar by the government for casting each vote. Mary the high school science teacher with $20,000 in net worth gets 200 votes, and earns $200 from the government for voting. Jeff Bezos, with $200 billion in net worth, gets 2 billion votes, and earns $2 billion from the government for voting. He’s a more valuable citizen than Mary, by a factor of a million, and also gets paid more by the government for already being wealthy.”
Additionally, despite a malicious validator can be punished by the system taking away its coins, it’s still possible (and easier than in PoW) to attack these networks for profit. Of course, as with PoW systems, the more users and validators have a network, the more expensive would be to attack it.
Decentralization in crypto services
Beyond the inner workings of a blockchain, there are a lot of crypto-related services outside of it. Analytics platforms, investment funds, wallets, exchanges. They are, in general, politically centralized, since they’re companies managed by a few and for profit. But we can talk about a decentralized architectural trick, in the case of exchanges.
In custodial cryptocurrency exchanges, the company fully controls the users’ funds while they’re inside its platforms. So, if this platform is hacked, seized, or somehow compromised, the users would probably lose their coins. Likewise, if the company decides to freeze those funds for any reason, they can also do it.

All of that can’t happen with non-custodial cryptocurrency exchanges like Alfacash. In these platforms, the users have full control of their private keys, and only send the exact amount they want to exchange whenever they want to trade it. This way is safer for all the parties, and respect this core feature of the cryptocurrency world: decentralization.
Wanna trade Bitcoin and other tokens? You can do it with decentralization on Alfacash! We’re talking about this and a lot of other things on our social media.
Twitter * Telegram * Facebook * Instagram * Youtube * Vkontakte








